Tag: security
-
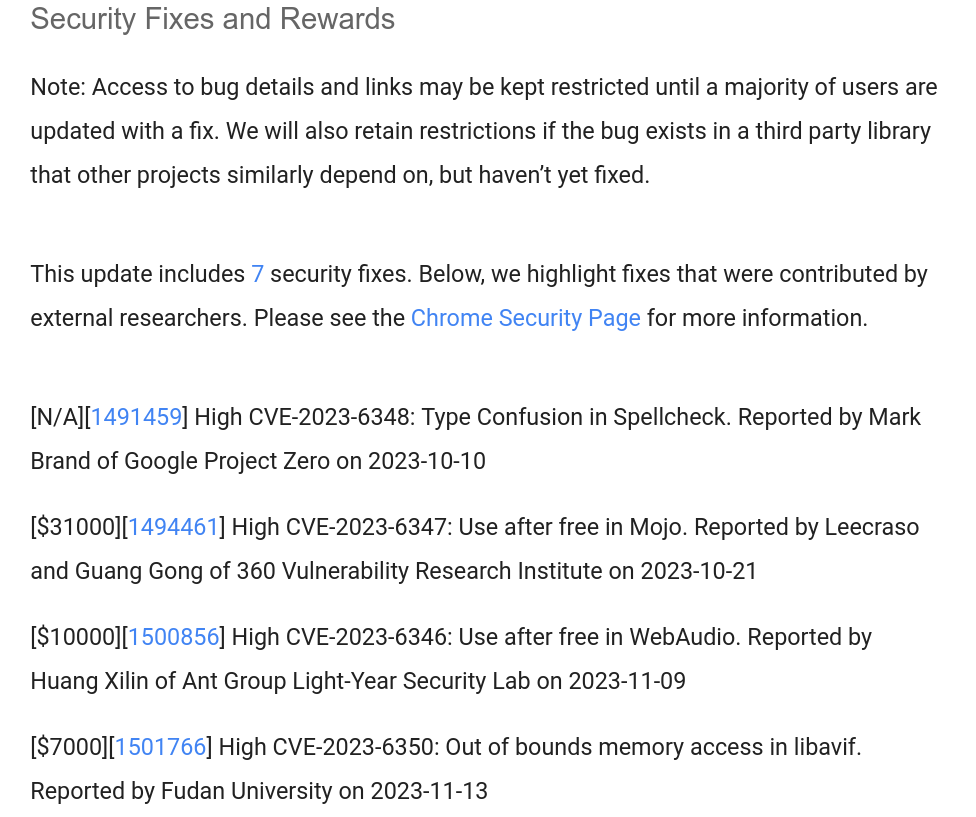
And I wondered why so many AUR package updates for the claude-code …
“Cybersecurity researchers have disclosed multiple security vulnerabilities in Anthropic’s Claude Code, an artificial intelligence (AI)-powered coding assistant, that could result in remote code execution and theft of API credentials.”
“The vulnerabilities exploit various configuration mechanisms, including Hooks, Model Context Protocol (MCP) servers, and environment variables – executing arbitrary shell commands and exfiltrating Anthropic API keys when users clone and open untrusted repositories”
https://thehackernews.com/2026/02/claude-code-flaws-allow-remote-code.html
-
If you’re using Tailscale with Mullvad VPN (either via the native Tailscale integration or standalone) and Firefox’s DNS over HTTPS (DoH), you might suddenly find yourself unable to access your Tailscale services via their
*.ts.nethostnames—even though everything worked fine before.The symptoms are frustrating:
tailscale pingworks,digresolves the hostname correctly, but Firefox just refuses to connect.Why This Happens
When you enable DNS over HTTPS in Firefox (especially with “Max Protection” mode), Firefox bypasses your system’s DNS resolver entirely and sends all DNS queries directly to your chosen DoH provider—in this case, Mullvad’s DNS server at
https://base.dns.mullvad.net/dns-query.The problem? Mullvad’s public DNS server has no idea what
my-server.my-tailnet.ts.netis. That’s a private hostname that only Tailscale’s MagicDNS (running at100.100.100.100) knows how to resolve.So while your system can resolve the hostname just fine:
$ dig my-server.my-tailnet.ts.net;; ANSWER SECTION:my-server.my-tailnet.ts.net. 600 IN A 100.x.x.x;; SERVER: 100.100.100.100#53(100.100.100.100) (UDP)Firefox completely ignores this and asks Mullvad instead, which returns nothing.
The Solution
Firefox provides a way to exclude specific domains from DoH, forcing it to fall back to system DNS for those domains. Here’s how to set it up:
- Open Firefox and navigate to
about:config - Search for
network.trr.excluded-domains - Add
ts.netto the list (comma-separated if there are existing entries)
For example:
ts.netOr if you have other exclusions:
example.local, ts.netThis tells Firefox: “For any domain ending in
.ts.net, use the system DNS resolver instead of DoH.” Since your system DNS is controlled by Tailscale’s MagicDNS, the hostname will resolve correctly.The Gotcha: Old Tailnet Names
Here’s a subtle issue that can trip you up: if you previously had a different Tailscale account or renamed your tailnet, you might have an old, specific exclusion that no longer applies.
For example, you might have:
my-nas.old-tailnet.ts.netBut your current tailnet is
new-tailnet.ts.net. The old exclusion does nothing for your new tailnet!The fix is simple: instead of excluding specific tailnet hostnames, just exclude the entire
ts.netdomain. This covers all Tailscale hostnames, regardless of your tailnet name, now and in the future.Verifying the Fix
After making the change, you can verify everything is working:
- Test Tailscale connectivity (should already work):
tailscale ping your-machine-name - Test DNS resolution from the command line:
dig your-machine-name.your-tailnet.ts.net - Test in Firefox: Navigate to your Tailscale hostname—it should now load.
Summary
If you’re combining Firefox DoH with Tailscale:
- Firefox’s DoH bypasses Tailscale’s MagicDNS
- Add
ts.nettonetwork.trr.excluded-domainsinabout:config - Use
ts.net(not a specific tailnet name) to future-proof the setting
This gives you the best of both worlds: private DNS for general browsing via Mullvad, and working hostname resolution for your Tailscale network.
- Open Firefox and navigate to
-
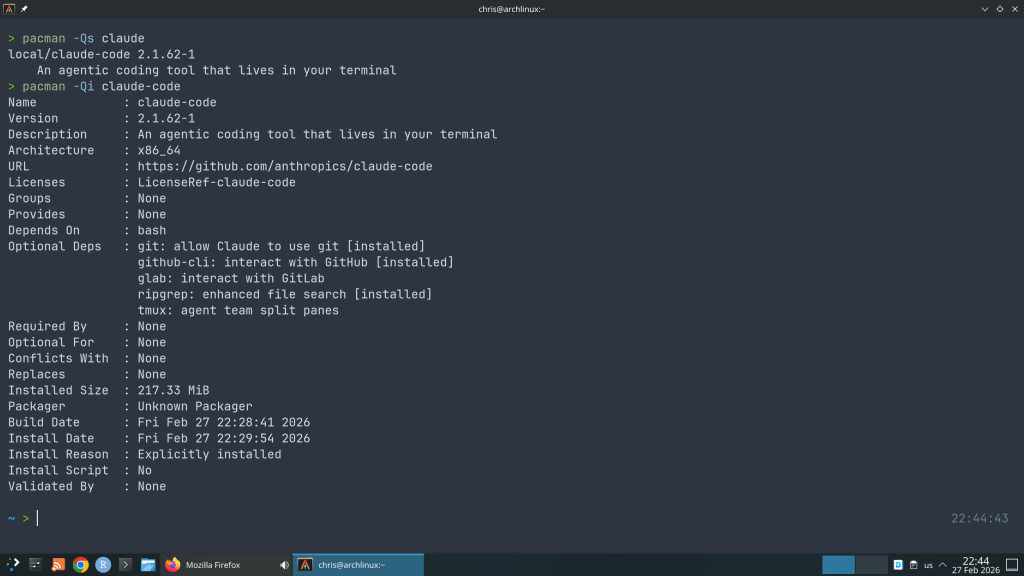
The most fascinating feature is the support for post-quantum cryptography (PQC) algorithms !!!
This release adds the following new features:
- Support for server side QUIC (RFC 9000)
- Support for 3rd party QUIC stacks including 0-RTT support
- Support for PQC algorithms (ML-KEM, ML-DSA and SLH-DSA)
- A new configuration option
no-tls-deprecated-ecto disable support for
TLS groups deprecated in RFC8422 - A new configuration option
enable-fips-jitterto make the FIPS provider
to use theJITTERseed source - Support for central key generation in CMP
- Support added for opaque symmetric key objects (EVP_SKEY)
- Support for multiple TLS keyshares and improved TLS key establishment group
configurability - API support for pipelining in provided cipher algorithms
https://github.com/openssl/openssl/releases/tag/openssl-3.5.0
-
“For being able to force additional CPU security mitigations even if the processor indicates it’s not vulnerable to a given bug like Spectre, Meltdown, Retbleed, and others.”

-
With over 750 commits over the last 2 years, previous xz versions are also not safe.

https://boehs.org/node/everything-i-know-about-the-xz-backdoor
-
- All supported FreeBSD releases include versions of xz that predate the affected releases.
- The main, stable/14, and stable/13 branches do include the affected version (5.6.0), but the backdoor components were excluded from the vendor import.
- Additionally, FreeBSD does not use the upstream’s build tooling, which was a required part of the attack. Lastly, the attack specifically targeted x86_64 Linux systems using glibc.
- The FreeBSD ports collection does not include xz/liblzma.
https://lists.freebsd.org/archives/freebsd-security/2024-March/000248.html
-
Seems pretty serious! Update your systems now !!!
The vulnerability affects xz packages prior to version 5.6.1-2 (specifically 5.6.0-1 and 5.6.1-1).
Andres Freund noticed odd symptoms around liblzma (part of the xz package) on Debian sid installations over the last weeks (logins with ssh taking a lot of CPU, valgrind errors) and concluded that the xz package has been backdoored.
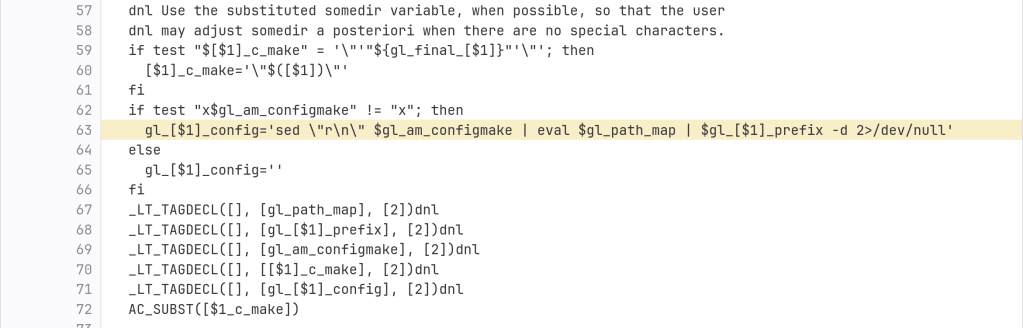
The backdoor is present in the tarballs released upstream and contains the following line (originally not present in the source code):
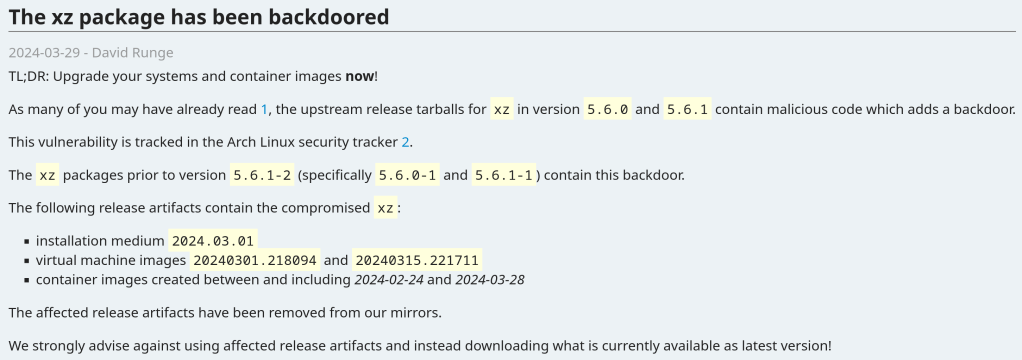
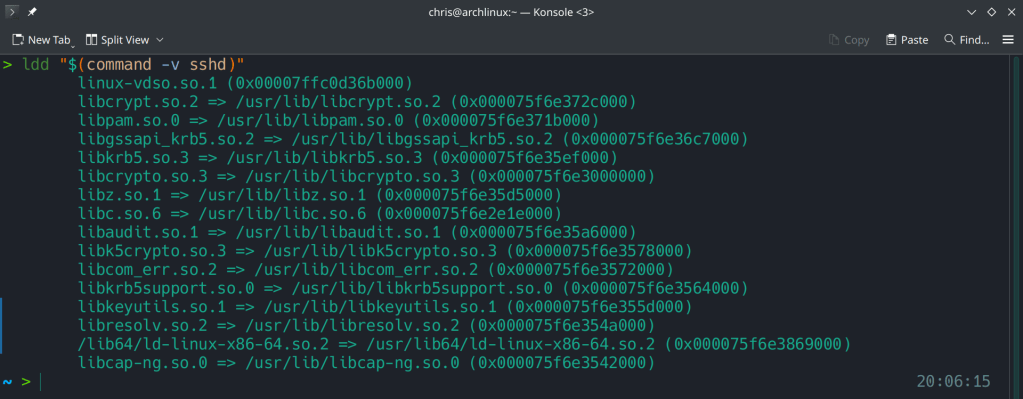
After the update:

Running ldd (shared libraries utility) to ensure no linkage between openssh and liblzma.
https://www.openwall.com/lists/oss-security/2024/03/29/4
https://archlinux.org/news/the-xz-package-has-been-backdoored
-
Among notable changes, this release includes a fix for the Terrapin Attack.

https://www.undeadly.org/cgi?action=article;sid=20231219122431
-
Brave, a browser focused on privacy installed a VPN service in Windows clients without even asking to do so. This behavior dates back to 2022 but is limited to the Windows version.
It’s possible to remove these services manually or another is to uninstall Brave and reinstall it without admin rights so that the program can’t install additional services.
https://www.theverge.com/2023/10/20/23925192/brave-browser-vpn-windows-11